Effective Cybersecurity in Practice
For over a decade, we have helped organizations stay ahead of evolving attack methods by continuously improving security operations. As adversaries adopt AI for greater speed, volume and sophistication, we must respond in kind. Delivering greater visibility, improved accuracy, faster response, and resilient operations.
01.
Rapid Deployment
Delivery speed matters. Consolidated, integrated architectures designed for maximum impact and low effort. We help you adopt new capabilities faster and keep pace with continuously evolving threats
02.
Human in the Loop
Setting goals, validating decisions, acting as guardrails are mandatory human-led activities. We design and engineer the technology workflows for consistency, accuracy and the intelligent use of AI
03.
Open Collaboration
Faster threat analysis and incident response improve cybersecurity ROI. We take the lead while working closely with your engineers, asset owners, and security teams to deliver enterprise-wide visibility and coordinated response
Cybersecurity solutions aligned to real-world operational requirements. Provided by U.S. citizens from U.S. based facilities.
Click for more information about everything we offer.
Continuous Threat Monitoring with Rapid Response
24×7 monitoring and response to detect, investigate, and contain threats before they disrupt operations. We ensure continuous, high-fidelity data collection to maintain complete visibility and reliable detection coverage. Every response is pre-approved, precise, and executed with minimal operational impact. For organizations of all sizes.
Key benefits
- Reduce organizational risk and improve resilience
- Access to latest security technology advancements
- Delivery from experienced security operations team
- Open collaboration at any time, for any purpose
- Predictable costs suitable for any size organization
Capabilities Include:
- Next Generation AI SIEM with SIEMaaS & EDR
- Security Operations with SOCaaS & MDR
- Extended coverage for cloud, identity and data
- Meet compliance with monitoring and retention
- Human led with AI augmentation
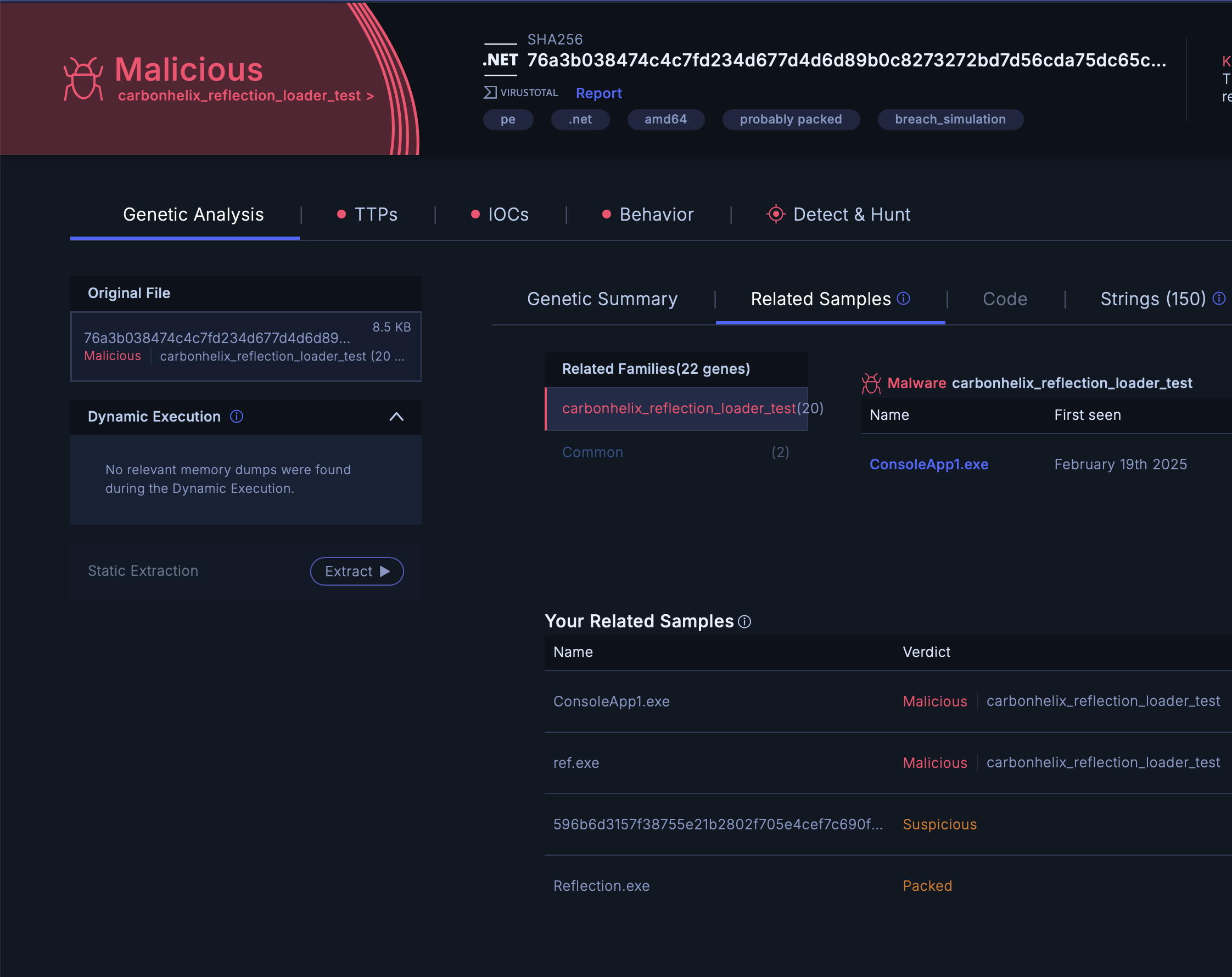
Attack Bypass Detection
Red team exercises consistently show that certain attack techniques will be missed or misclassified, resulting in latent, currently undetected compromise. As adversaries increasingly leverage AI trained on offensive tradecraft, detection efficacy is expected to decline in the absence of equally advanced defensive counter measures. Our approach uses trigger events, such as EDR alerts, as pivot points for deeper artifact analysis, enabling us to identify missed detections and remove ambiguity around the true impact and scope of each alert.
Key benefits
- Uncover latent infections before the breach
- Validate alerts as true or false positives for tuning
- Triage alerts with greater confidence and accuracy
- Indicator expansion with threat relationships
- AI forensics for genetic analysis of artifacts
Capabilities Include:
- Endpoint bypass detection from EDR alerts
- Email bypass detection from Phish alerts
- General bypass detection from Backup alerts
- Other Trigger Events including SIEM alerts
- Eliminates ambiguity from investigations
Continuous Clean Backup Validation
In the event of a breach, cyber resilience solutions are used to pinpoint the most recent clean backup verified to be free of infection. Our continuous scanning of your backups accelerates recovery timelines, but more importantly, helps prevent full-scale breaches by uncovering latent infections that evaded earlier detection. The same capability is also applied on a scheduled basis across other data repositories and file systems to automatically identify and surface hidden threats.
Key benefits
- Prevent infections from becoming breaches
- Identify the clean restore point before needed.
- Uncover infected systems that have missed detection
- Understand the full impact of latent infection
Capabilities Include:
- Connects to your own backup products
- Uses your own data repositories
- Includes private AI forensics sandbox
- Optional cloud backup service is available
Data Security
Data security helps organizations discover sensitive data, monitor access and activity, reduce risk, and respond quickly across hybrid environments. Customers gain stronger visibility into data location and risk, expert-led operations, and practical support for compliance, retention, and ongoing data protection.
Key benefits
- Reduce enterprise-wide data exposure risk
- Improve compliance readiness and visibility
- Monitor sensitive data across environments
- Accelerate detection and guided response
- Automate workflows for rapid response
Capabilities Include:
- Sensitive data discovery and classification
- Continuous activity monitoring and alerting
- Risk-based exposure analysis and prioritization
- Investigation and response workflow support
- Coverage across cloud, SaaS, on-prem
Multi-Platform Security Overlay with Alert Correlation
Our unified operational and engineering layer, repurposed to support organizations that run multiple SIEM, EDR/XDR, and security tools across departments, business units, regions, or IT/OT domains. It enables centralized visibility and consistent detection without requiring consolidation to a single SIEM, EDR, threat detection platform or Agentic AI.
Key benefits
- Insight into how threats target multiple domains
- Natural language search across toolsets and data.
- Predict the next attack target, and prepare.
- AI applied consistently with governance and controls.
- Unified multi-site security posture awareness
Capabilities Include:
- Centralized oversight of all security deployments
- Alert correlation, visibility across tools and sites
- Unified threat hunting across all environments
- Shared threat intelligence and alert enrichment
- Alert normalization for incident comprehension
Predictive Attack Intelligence
Threat Actors use of Adversarial AI this year will drive more sophisticated attacks, with greater frequency, exploit speed and volume. Inevitably this will lead to some bypass, detection misses and latent infections. We use defined trigger events to run AI forensics and IOC expansion playbooks to build a more complete picture of the relationship between an observed IOC and the threat actors, campaigns and malware families behind it. We can also trigger on vulnerability CVE for retroactive hunts of attempted exploit activity in your environment.
Key benefits
- Predict attacks and begin to monitor for activity
- Understand the full impact of observed indicators
- Prioritize specific defenses at a lower cost earlier
- Begin threat hunting with targeted precision
- Free analysts from routine research tasks
Capabilities Include:
- Threat relationship mapping with AI assist
- IOC expansion from observed IOC / TTP
- CVE to IOC expansion from KEV or CVE notifications
- Forensics expansion with our private AI sandbox
- Rapid AI-driven CTI research and reporting
Remote Workforce Secure Access
Secure, high-speed remote access for a distributed workforce, connecting users directly to applications with minimal delay and strong security controls. Access is limited to only the applications users are authorized to use, based on identity and device trust. Every session is continuously verified, monitored, and protected to prevent threats and unauthorized activity, delivering a simple user experience with full visibility and control across both cloud and on-premises environments.
Key benefits
- Improved user experience with fast regional access
- Detailed visibility and telemetry for analytics
- Simple, easy deployment with modern ZTNA / SASE
- Reduced attack surface with continuous verification
Capabilities Include:
- Modern zero-trust access compared with legacy VPN
- Endpoint device posture enforcement
- User and Identity posture enforcement
- Application level controls and segmentation
Identity Security Monitoring
We help organizations secure human, non-human, and AI agentic identities by strengthening access, detecting misuse, and containing threats faster across workforce, privileged, application, and machine accounts.
Key benefits
- Protect every identity type consistently
- Reduce exposure from compromised accounts
- Improve control over privileged access
- Detect misuse across modern environments
- Strengthen resilience against identity attacks
Capabilities Include:
- Authentication and adaptive access enforcement
- Monitoring human and machine identities
- Oversight for AI agentic identities
- Behavioral detection for suspicious activity
- Coordinated containment and incident handling
High-Fidelity AI Triage
AI triage is not a one-time event to reduce alert volume, it is applied continuously across multiple stages of SOC workflows to improve detection, prioritization, and investigation.
It combines techniques across platforms to deliver deeper insight into security incidents by: Reprioritizing alerts through dynamic scoring and grouping of related activity observed across environments. Mapping attack patterns by correlating dissimilar alerts into a unified attack chain over time. Continuously refining severity using enrichment, analyst feedback, and re-analysis of the evidence.
AI triage can also be applied to lower-level alerts, enabling earlier detection in the attack lifecycle while improving true positive accuracy and reducing false positives.